Blog
Security
/ 1 Jun, 2026Analysis of the 2026 Stryker Breach: Weaponizing Cloud Endpoint Management
On March 11, 2026, attackers turned Stryker Corporation's own Microsoft Intune device-management plane into a non-encrypting wiper, factory-resetting roughly 200,000 endpoints across 79 offices worldwide without dropping a single piece of custom malware.
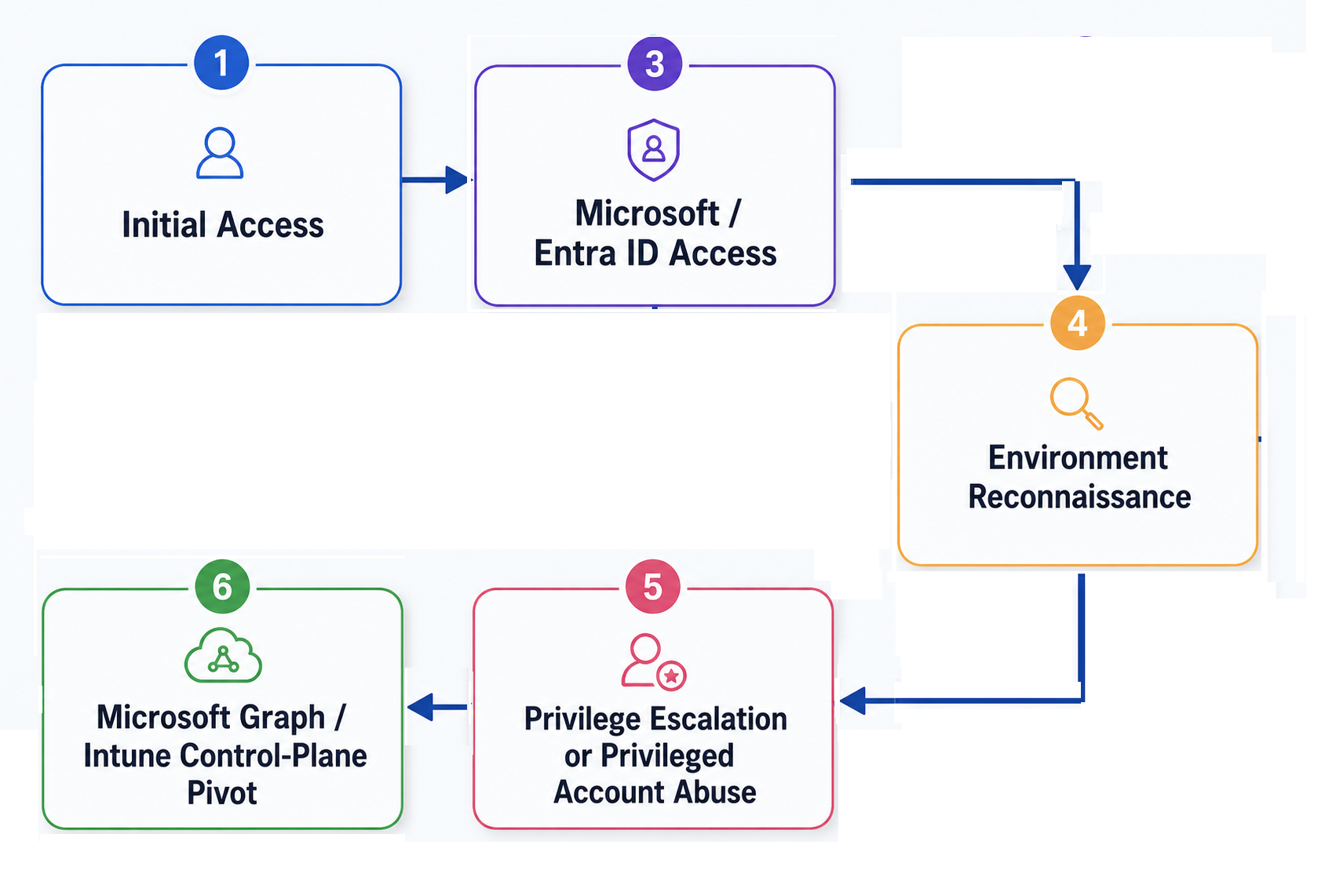
This analysis reconstructs the Living-off-the-Land attack chain — from infostealer logs and AiTM session theft through privilege escalation to the Intune control-plane pivot — and shows how SlashID's MITM/AiTM detection, phishing-resistant authentication, behavioral anomaly detection, and just-in-time privileged access stop it.
Security
/ 1 Jun, 2026Analysis of the 2026 Stryker Breach: Weaponizing Cloud Endpoint Management
On March 11, 2026, attackers turned Stryker Corporation's own Microsoft Intune device-management plane into a non-encrypting wiper, factory-resetting roughly 200,000 endpoints across 79 offices worldwide without dropping a single piece of custom malware.
This analysis reconstructs the Living-off-the-Land attack chain — from infostealer logs and AiTM session theft through privilege escalation to the Intune control-plane pivot — and shows how SlashID's MITM/AiTM detection, phishing-resistant authentication, behavioral anomaly detection, and just-in-time privileged access stop it.


Open Source
/ 12 Nov, 2022Adding Identity to Docusaurus
Today we are releasing the docusaurus-slashid-login theme as well as a fork of docusaurus-openapi-docs.
The slashid plugin enables you to add out of the box authentication to docusaurus. The docusaurus-openapi-docs fork allows you to autofill API keys data, API parameters and more through slashid user attributes.


New Feature
/ 7 Nov, 2022Introducing Data Vault - Secure HSM-backed PII storage directly from the frontend
Today we are releasing Data Vault, which allows the safe and compliant storage of sensitive user data directly from the frontend.
Data Vault takes care of data localization and protection transparently, without having to build ad-hoc infrastructure to handle encryption or key management and rotation.


New Feature
/ 1 Nov, 2022Social logins in 5 minutes or less
Today we are releasing our OpenID Connect (OIDC) SSO module which you can use to add Social logins and OIDC-compatible SSO to your app in less than 5 minutes.
Social logins can significantly boost user registration - for instance, Pinterest reported a 47% registration increase after adding Google One Tap to their website.


Deep Dives
/ 20 Oct, 2022App-layer cryptographic primitives for secure storage of user data
In this blogpost we explore the cryptographic primitives and design decisions we made building our Data Vault module.
Our service is a globally replicated, field-level encrypted, data store to keep user data safe and compliant with Data Protection laws while improving UX by decreasing latency through data locality.


Deep Dives
/ 23 Sep, 2022The good, the bad and the ugly of Apple Passkeys
The widely anticipated Apple passkeys launch happened just a few weeks ago with the iOS 16 release.
Passkeys are a cross-device extension of FIDO credentials compatible with WebAuthn. They address the main UX issue of WebAuthn, cross-device credentials.
In this article we’ll explore the Apple passkeys implementation, how passkeys compare to traditional FIDO credentials and why the decision of Apple to get rid of device attestation and resident keys is a significant step back for security.


Compliance
/ 14 Sep, 2022The Security and Regulatory Compliance Benefits of WebAuthn
The WebAuthn standard helps you stop phishing and account takeover (ATO) attacks while maintaining HIPAA and SCA compliance.
WebAuthn is significantly safer than passwords, due to the way the keys are stored and because it prevents credential stuffing and reuse attacks.


Security
/ 12 Sep, 2022Phishing Attacks – WebAuthn to the rescue
Authentication token theft is on the rise, with the latest Uber breach demonstrating yet again the threat that it poses.
WebAuthn significantly reduces user experience friction and hence allows for more frequent authentication prompts, offsetting the need for long-lived tokens and significantly curbing the risk of phishing.



