Blog
Security
/ 1 Jun, 2026Analysis of the 2026 Stryker Breach: Weaponizing Cloud Endpoint Management
On March 11, 2026, attackers turned Stryker Corporation's own Microsoft Intune device-management plane into a non-encrypting wiper, factory-resetting roughly 200,000 endpoints across 79 offices worldwide without dropping a single piece of custom malware.
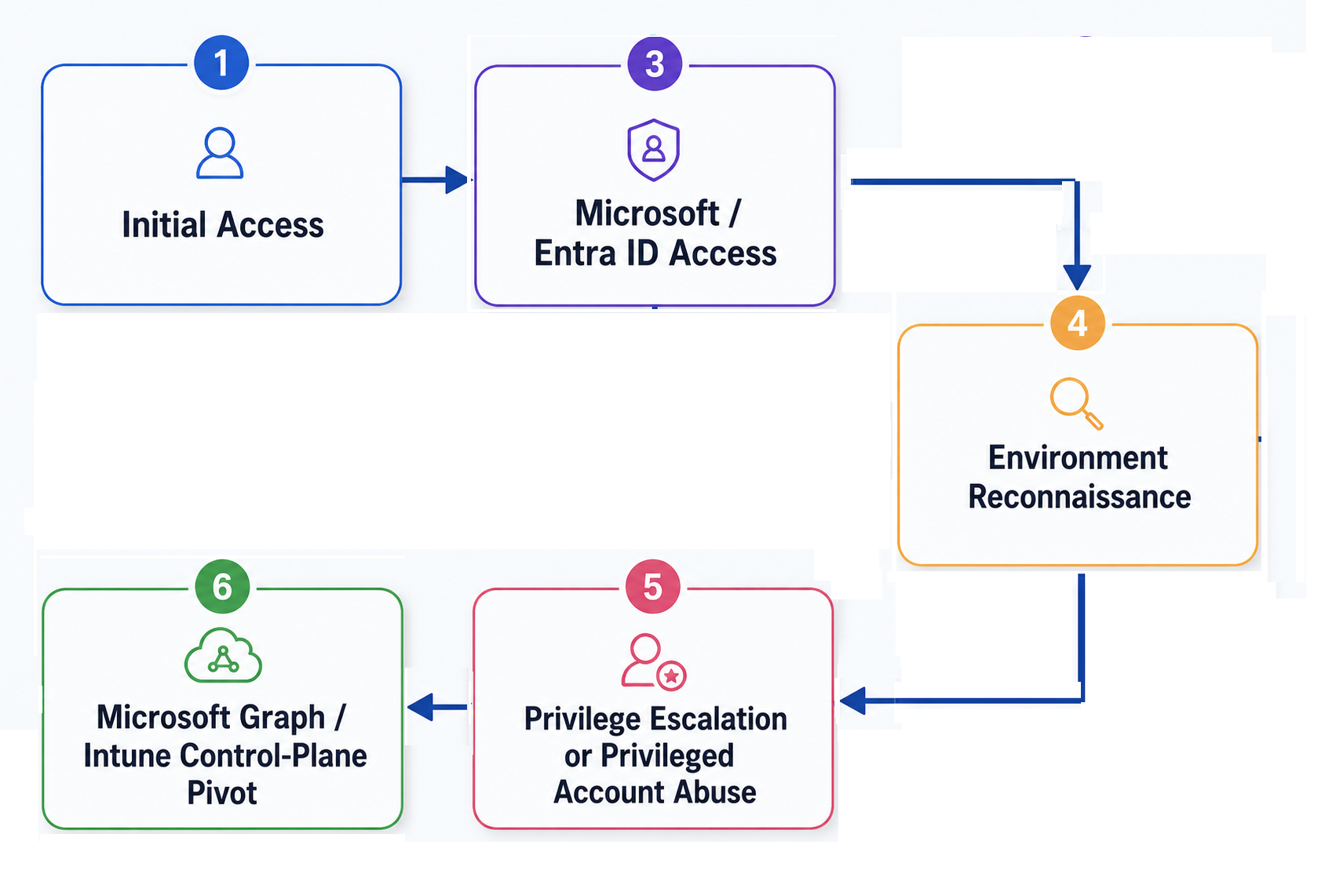
This analysis reconstructs the Living-off-the-Land attack chain — from infostealer logs and AiTM session theft through privilege escalation to the Intune control-plane pivot — and shows how SlashID's MITM/AiTM detection, phishing-resistant authentication, behavioral anomaly detection, and just-in-time privileged access stop it.
Security
/ 1 Jun, 2026Analysis of the 2026 Stryker Breach: Weaponizing Cloud Endpoint Management
On March 11, 2026, attackers turned Stryker Corporation's own Microsoft Intune device-management plane into a non-encrypting wiper, factory-resetting roughly 200,000 endpoints across 79 offices worldwide without dropping a single piece of custom malware.
This analysis reconstructs the Living-off-the-Land attack chain — from infostealer logs and AiTM session theft through privilege escalation to the Intune control-plane pivot — and shows how SlashID's MITM/AiTM detection, phishing-resistant authentication, behavioral anomaly detection, and just-in-time privileged access stop it.


Security
/ 17 Jun, 2024ODPR: A Framework for Securing Non-Human Identities
Identity-based attacks have become the primary way attackers move laterally in a network. They are also responsible for half of the initial intrusions.
Addressing these attacks requires very different tooling and approaches compared to malware-based attacks.
In this article we delve into the SlashID framework to address these attacks.


New Feature
/ 10 Jun, 2024Credential Tokenization: Protecting third-party API credentials
Stolen secrets and credentials are one of the most common ways for attackers to move laterally and maintain persistence in cloud environments.
In this blog post we introduce credential tokenization to protect secrets at runtime, introduce separation of duties, and reduce the credential rotation burden.


New Feature
/ 3 Jun, 2024Secure API and M2M Access with OAuth2 Client Credentials and SlashID's sidecar
The recent Hugging Face breach is yet another reminder that securing machine-to-machine communication and API access is essential today.
By leveraging OAuth2 Client Credentials, you can enhance security, enable fine-grained access control, simplify credential management, and benefit from a standards-based approach.


New Feature
/ 14 May, 2024Introducing Organization Attributes
With organization attributes, you can now easily store and manage tenant-level data directly on our platform.


New Feature
/ 24 Apr, 2024Introducing Anonymous Users: Balancing First-Party Data Collection and User Experience
With the deprecation of third-party cookies, first-party data has become crucial for websites to personalize user experiences.
SlashID introduces Anonymous Users, a feature that allows websites to collect user data without forcing users to register or log in, striking the perfect balance between data collection and user experience.


Product Releases
/ 2 Apr, 2024SlashID SDK for PHP and Laravel authentication
While very popular, PHP lacks modern identity and access management (IAM) capabilities. SlashID changes that with the release of our SDK for PHP and Laravel.
This is just the beginning; according to W3Tech PHP is used by over 76% of indexed websites. In the weeks to come, we aim to cover other popular frameworks such as Drupal and Symfony.


Deep Dives
/ 6 Mar, 2024Adding custom claims to identity tokens
Adding custom claims to JWTs allows you to share identity information without repeated queries to external data sources.
Read on to learn how to customize claims with SlashID's webhooks.


New Feature
/ 19 Feb, 2024SlashID: Building a globally distributed Identity Platform
We built the SlashID infrastructure so that your user data is globally distributed.
Our architecture helps applications using SlashID benefit from dramatically reduced latency, high availability and comply with data protection laws without fragmented identity silos or extra fees.


Deep Dives
/ 31 Jan, 2024Passkeys Adoption Trends: Survey from Large Deployments
In this comprehensive blog post, we delve into the publicly available data on large-scale passkeys rollouts, examining results, conversion rates, and implementation challenges as documented in engineering blogs by companies like Kayak and Yahoo Japan.



