Blog
Security
/ 1 Jun, 2026Analysis of the 2026 Stryker Breach: Weaponizing Cloud Endpoint Management
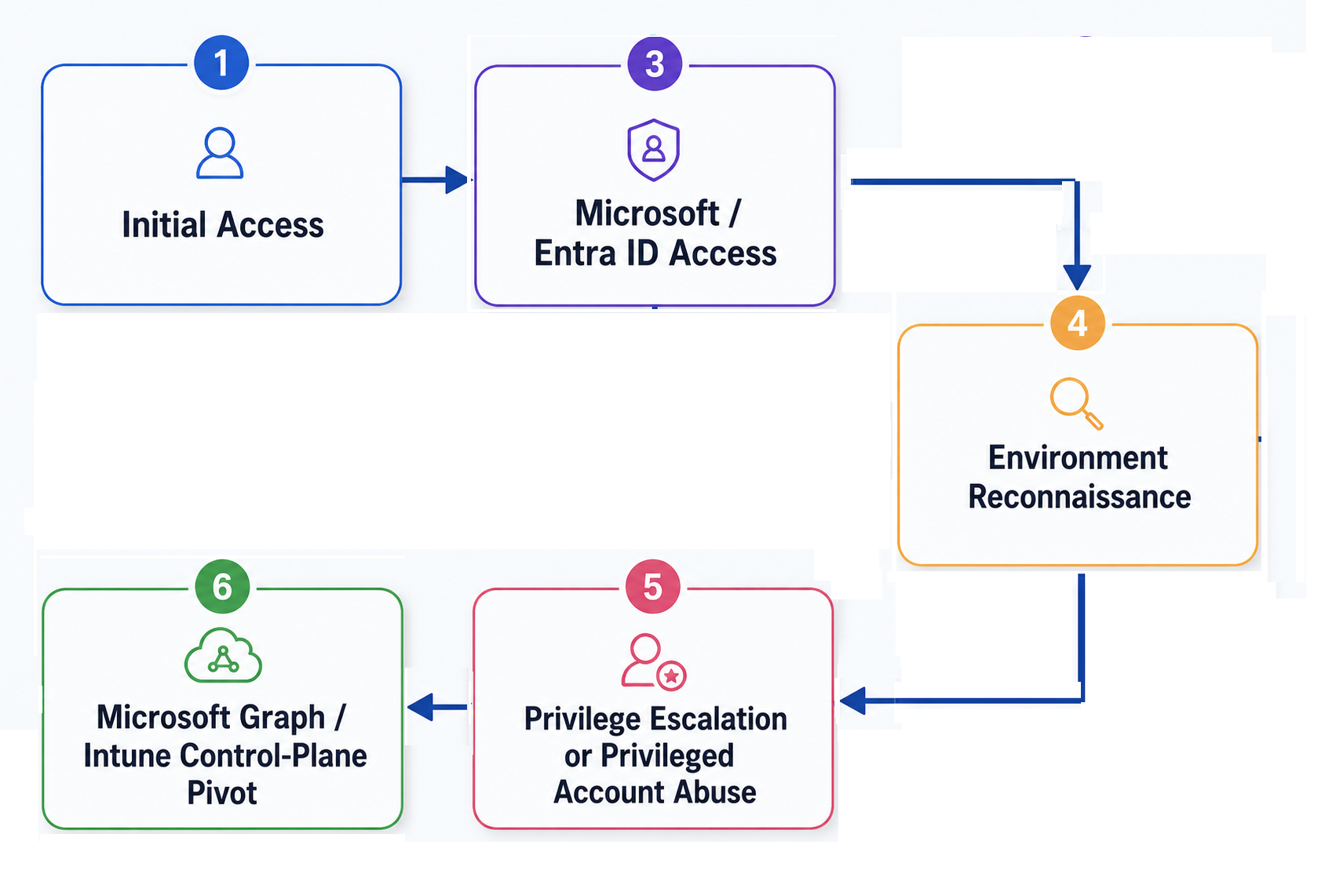
On March 11, 2026, attackers turned Stryker Corporation's own Microsoft Intune device-management plane into a non-encrypting wiper, factory-resetting roughly 200,000 endpoints across 79 offices worldwide without dropping a single piece of custom malware.
This analysis reconstructs the Living-off-the-Land attack chain — from infostealer logs and AiTM session theft through privilege escalation to the Intune control-plane pivot — and shows how SlashID's MITM/AiTM detection, phishing-resistant authentication, behavioral anomaly detection, and just-in-time privileged access stop it.
Security
/ 1 Jun, 2026Analysis of the 2026 Stryker Breach: Weaponizing Cloud Endpoint Management
On March 11, 2026, attackers turned Stryker Corporation's own Microsoft Intune device-management plane into a non-encrypting wiper, factory-resetting roughly 200,000 endpoints across 79 offices worldwide without dropping a single piece of custom malware.
This analysis reconstructs the Living-off-the-Land attack chain — from infostealer logs and AiTM session theft through privilege escalation to the Intune control-plane pivot — and shows how SlashID's MITM/AiTM detection, phishing-resistant authentication, behavioral anomaly detection, and just-in-time privileged access stop it.


Deep Dives
/ 21 Sep, 2023JWT Implementation Pitfalls, Security Threats, and Our Approach to Mitigate Them
JSON Web Tokens (JWTs) are one of the most common ways to transfer identity claims and prove the identity of a user or an entity. JWTs have become very popular in recent years because they are easy to use, read, and debug.
JWTs provide a lot of flexibility at the expense of several security risks that are often overlooked. In this article, we'll discuss common risks when implementing or manipulating JWTs and our approach to avoiding them.


Tutorial
/ 18 Sep, 2023No-code anti-phishing protection of internal apps with Passkeys
Phishing is one of the most common causes of data breaches. According to Verizon's DBIR report, over 50% of incidents start with phishing or stolen credentials. WebAuthn/Passkeys are an effective way to stop phishing and credential stealing attempts on their tracks.
In this article, we’ll show how you can use Gate to enforce Passkeys authentication for users without modifying the application code.


Tutorial
/ 14 Sep, 2023Firewalling OpenAI APIs: Data loss prevention and identity access control
Large Language Models (LLMs) have taken the world by storm, and they are now used for many tasks by consumers and enterprises alike. However, the risk of accidentally disclosing sensitive data to the models is very high as the recent Samsung case shown.
In this article, we’ll show how you can use Gate to detect sensitive data in requests sent to the OpenAI APIs, as well as enforcing access control so that only users with certain roles can access the APIs.


New Feature
/ 12 Sep, 2023Ditch your organizations table
Suborgs make it effortless and secure to implement complex identity structures such as multi-tenancy B2B apps and multi sided marketplaces.


Tutorial
/ 5 Sep, 2023Protecting Exposed APIs: Avoid Data Leaks with SlashID Gate and OPA
Adequately protecting APIs is key to avoid data leaks and breaches.
Just recently, an exposed API allowed an attacker to scrape over 2.6 million records from Duolingo.
In this article, we’ll show how you can use Gate to detect, respond to, and prevent these kinds of incidents.


Open Source
/ 28 Aug, 2023Docusaurus - Authentication and authorization with SlashID
The latest docusaurus-slashid-login theme adds finer grained access control to your Docusaurus website.


New Feature
/ 25 Jul, 2023Authenticate your Shopify customers with SlashID
The new SlashID Login app for Shopify lets your customers authenticate seamlessly using quick and safe methods like passkeys, social login and magic links.


New Feature
/ 20 Jul, 2023Synchronous Webhooks
We are excited to release synchronous webhooks, the latest addition to our webhooks features.
With synchronous webhooks, you can extend SlashID Access to suit your business needs in a few simple steps, in whatever language and environment makes sense for you.


Tutorial
/ 16 Jul, 2023Building a React Login Page Template
Discover how to create a secure login page for your React app with authentication and styling using SlashID.



