Blog
Security
/ 1 Jun, 2026Analysis of the 2026 Stryker Breach: Weaponizing Cloud Endpoint Management
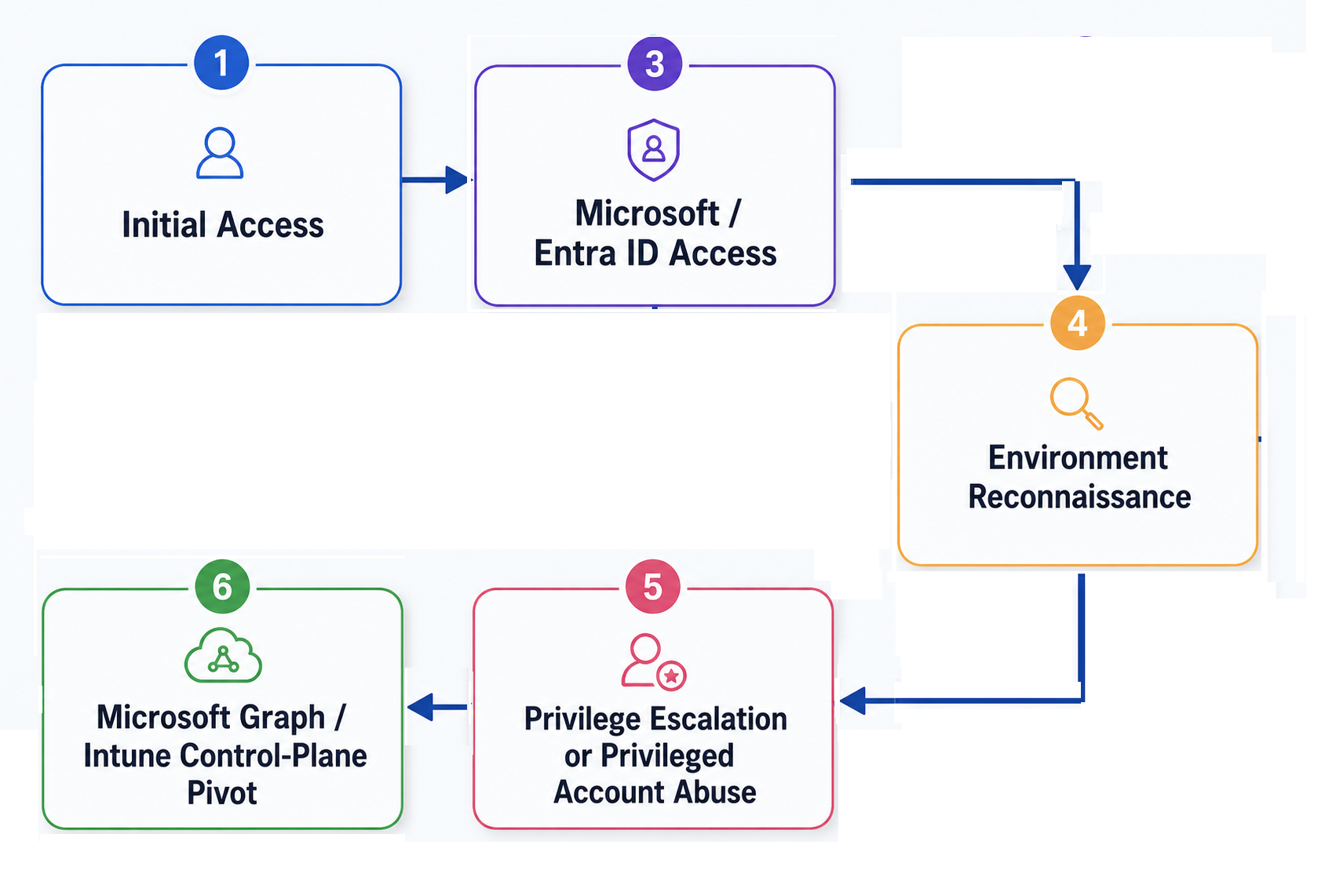
On March 11, 2026, attackers turned Stryker Corporation's own Microsoft Intune device-management plane into a non-encrypting wiper, factory-resetting roughly 200,000 endpoints across 79 offices worldwide without dropping a single piece of custom malware.
This analysis reconstructs the Living-off-the-Land attack chain — from infostealer logs and AiTM session theft through privilege escalation to the Intune control-plane pivot — and shows how SlashID's MITM/AiTM detection, phishing-resistant authentication, behavioral anomaly detection, and just-in-time privileged access stop it.
Security
/ 1 Jun, 2026Analysis of the 2026 Stryker Breach: Weaponizing Cloud Endpoint Management
On March 11, 2026, attackers turned Stryker Corporation's own Microsoft Intune device-management plane into a non-encrypting wiper, factory-resetting roughly 200,000 endpoints across 79 offices worldwide without dropping a single piece of custom malware.
This analysis reconstructs the Living-off-the-Land attack chain — from infostealer logs and AiTM session theft through privilege escalation to the Intune control-plane pivot — and shows how SlashID's MITM/AiTM detection, phishing-resistant authentication, behavioral anomaly detection, and just-in-time privileged access stop it.


Security
/ 8 Jan, 2025Protecting against malicious OAuth 2.0 applications
Several Chrome extension developers were compromised in recent weeks by an attack seeking to create a backdoor in the
extensions.
The root cause of the breach was a phishing email that leveraged OAuth 2.0/OIDC to steal
the user credentials.
This blog post explores the details of such attacks and how SlashID can help detect them and contain
the blast radius.


Security
/ 16 Dec, 2024Navigating PCI DSS 4.0: The Challenge of Non-Human Identities
The Payment Card Industry Data Security Standard (PCI DSS) has long served as the foundation for organizations handling payment card data, ensuring robust security measures are - in place to protect sensitive information
The release of PCI DSS version 4.0 on March 31, 2022, marked a significant evolution in the standard, introducing requirements and emphasizing areas that were previously under-addressed.
One such critical area is the management of non-human identities—service accounts, application accounts, APIs, and automated scripts that interact with cardholder data environments (CDE) or critical systems.
With the deadline of March 2025 fast approaching, we wrote a blog post to delves into the specific challenges companies face regarding non-human identities in PCI DSS v4.0 and - explores strategies to overcome them.

Security
/ 30 Sep, 2024Identity Security: The problem(s) with federation
Federating trust with an identity provider (IdP) is common practice to centralize identity governance.
However, attackers can exploit identity federation to breach organizations or maintain persistence in a system.
This blog post explores common attack vectors against federated identities and effective mitigation strategies.


Security
/ 16 Sep, 2024Non-Human Identities Security: Breaking down the problem
Compromised non-human identities are increasingly being leveraged by attackers to gain initial access and as a vector for lateral movement.
Microsoft, Cloudflare, and Dropbox are just a few of the companies that have fallen victim to this growing threat this year.
In this blog post, we focus on the attack vectors involved and on what actions companies must take to prevent these attacks.


New Feature
/ 26 Aug, 2024Detecting Man-in-the-Middle Attacks with SlashID
Detect when attackers access your website through malicious proxies with SlashID.


Deep Dives
/ 22 Aug, 2024A deep dive in the AWS credential leaks reported by Palo Alto Networks
Thousands of credentials were exfiltrated from exposed .env files in the latest large-scale attack uncovered by Palo Alto.
Protecting cloud services and non-human identities spread across many vendors and environments is now table-stakes: SlashID can help.


New Feature
/ 22 Jul, 2024SlashID RBAC: Globally-available role-based access control
SlashID RBAC is a globally replicated role-based access control system that allows you to restrict access to resources based on permissions assigned to specific persons.
In this post, we will show you how to use RBAC in SlashID, and how to create permissions, and roles, and assign them to persons.


Security
/ 15 Jul, 2024Protecting against Snowflake breaches
In the last few weeks several very high-profile breaches have been in the news, from Santander to Ticketmaster and AT&T.
These breaches all have the same attack vector: identity-based attacks against Snowflake instances.
In this article, we discuss the causes of the breach and our approach to protect against identity-based attacks against Snowflake.


New Feature
/ 24 Jun, 2024Introducing the SlashID Local Deployment
The SlashID local deployment is our answer for developers looking to build, run and test apps locally.
Local development with SlashID can be a good fit for your evaluation, prototyping, development, and continuous integration workflows.



